Troubleshoot
If you need further assistance setting up GitOps, feel free to reach us.
General
- Bytebase only observes merge event. If the file is pushed to the branch directly, it will be ignored.
- Migration file must follow the path and naming convention.
- Bytebase has configured a proper External URL and the URL is network accessible from VCS.
Bytebase observes the VCS merge event via webhook. The created webhook link is on the top of the Git connector setting page.
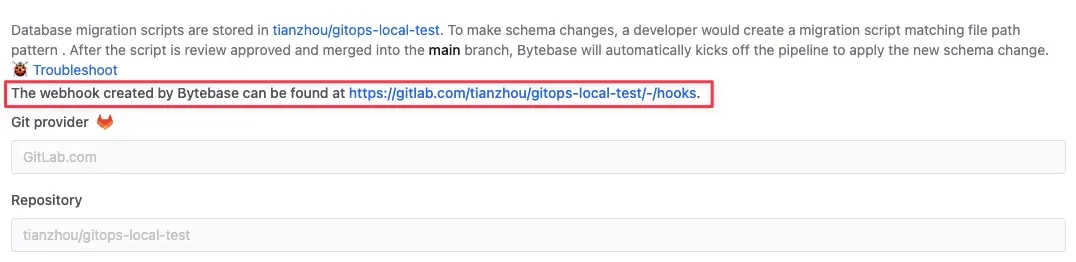
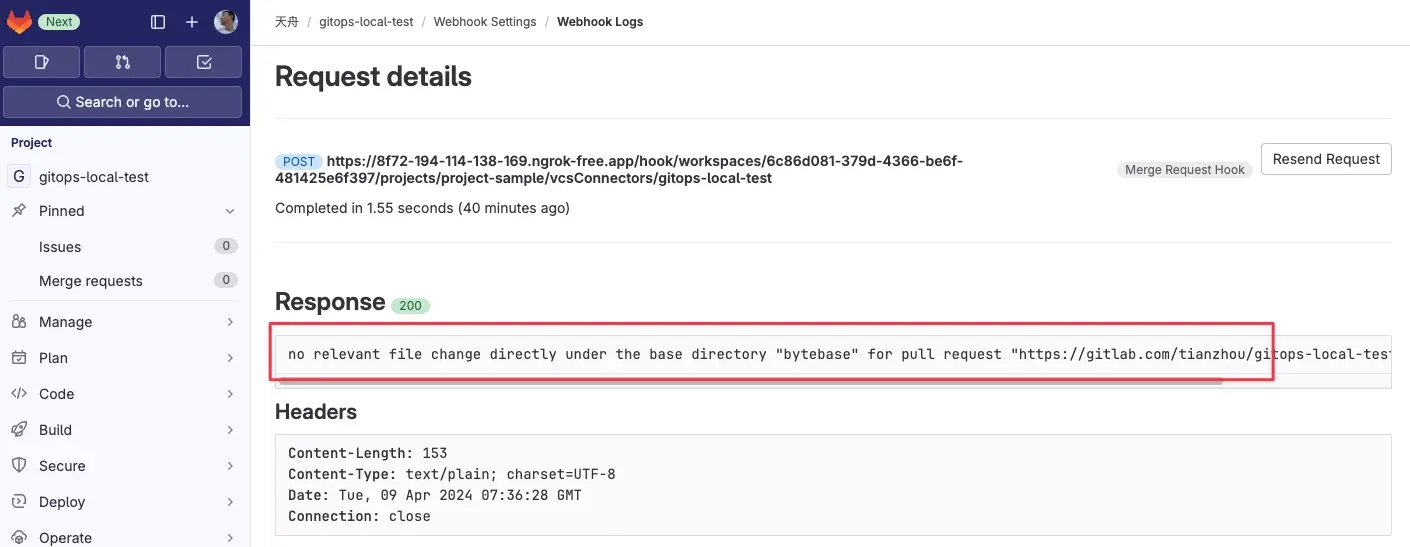
Check the webhook running history to debug the reason.
GitLab
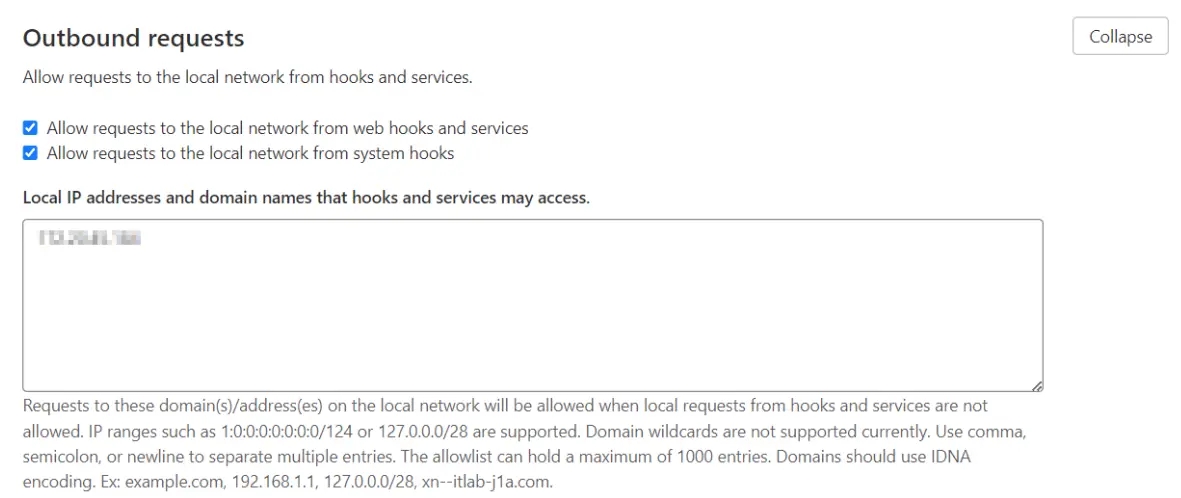
Failed to create webhook xxx, status code: 422
If you configure External URL with the private IP such as 10.0.0.0/8, 172.16.0.0/12, 192.168.0.0/16, you will need to enable Allow requests to the local network from webhooks and integrations first.
INVALID_ARGUMENT: failed to fetch repositories
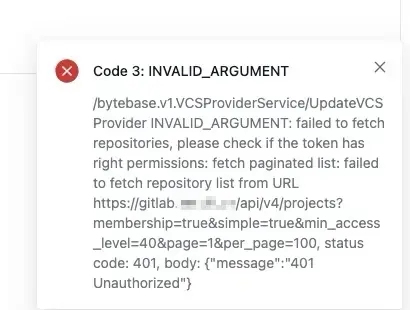
If your GitLab is before 12.2, then the personal access token won't work and you need to use the OAuth token to configure the GitLab Provider